For years, critical Infrastructure such as defense, utilities and telecommunications have been “under siege” – operating under a constant threat of cyberattack. From the Colonial Pipeline attack to the rise of nation-state attacks, these escalating risks have recently been documented in the 2022 Thales Data Threat Report: Critical Infrastructure Edition.
In response to this evolving threat landscape, US Congress recently passed the Cyber Incident Reporting for Critical Infrastructure Act of 2022 (CIRCIA) – a law under which entities who own or operate critical infrastructure facilities will be required to report certain cybersecurity incidents to the Cybersecurity and Infrastructure Security Agency (CISA) within set timeframes.
While these required data reports will prove invaluable to the intelligence community and the public at large – some facility owners and operators are concerned that for them, the medicine could be worse than the disease.
For operators wanting to understand the new bill and have a voice in determining their reporting obligations – there are ways to prepare, as well as potentially minimize – CIRCIA’s impacts on business operations.
Reporting requirements under CIRCIA – an overview
CIRCIA requires the entities that run critical infrastructure to submit a report within 72 hours of an incident. Depending how CISA ultimately administers the law, this requirement could challenge operators with potentially unmanageable reporting burdens. For example, if a botnet launches 1,000 related attacks against a power grid, is that one incident or 1,000? If the attacks are launched sequentially between 3:10 to 3:20 a.m. on a Friday, will a grid operator be legally required to submit 1,000 reports before dawn the following Monday?
Congress has opted not to answer questions like these in the bill. CIRCIA leaves key terms such as “covered cybersecurity incident” intentionally undefined. Nor does the law say exactly which entities are beholden to the reporting requirements.
Instead, Congress has charged the director of CISA, in consultation with other federal agencies and public stakeholders, with developing precise definitions and detailed reporting procedures.
Q-Net Security CEO Ron Indeck welcomed the public consultation process.
“By allowing industry to collaborate with the government in shaping the final rules, there is a good chance that what we end up with will be a reasonable fit,” he said.
This is where operators of critical infrastructure and their staff have a chance to actively shape the reporting guidelines - and prepare for the future - by:
1) Helping CISA craft manageable guidelines, by having their say.
2) Building tougher cyber defenses into their facilities, to reduce reportable incidents overall.
Help CISA craft manageable guidelines
CISA is offering two opportunities for public input as they develop the reporting rules pertaining to CIRCIA. First, citizens may file formal written comments online through CISA’s Request for Information database. Commenting will remain open through November 14.
Written comments will be most persuasive if they are clear, concise, and data-driven. Commenters should refer to their credentials and cite their sources. Brief stories or anecdotes may help to land an otherwise dry point.
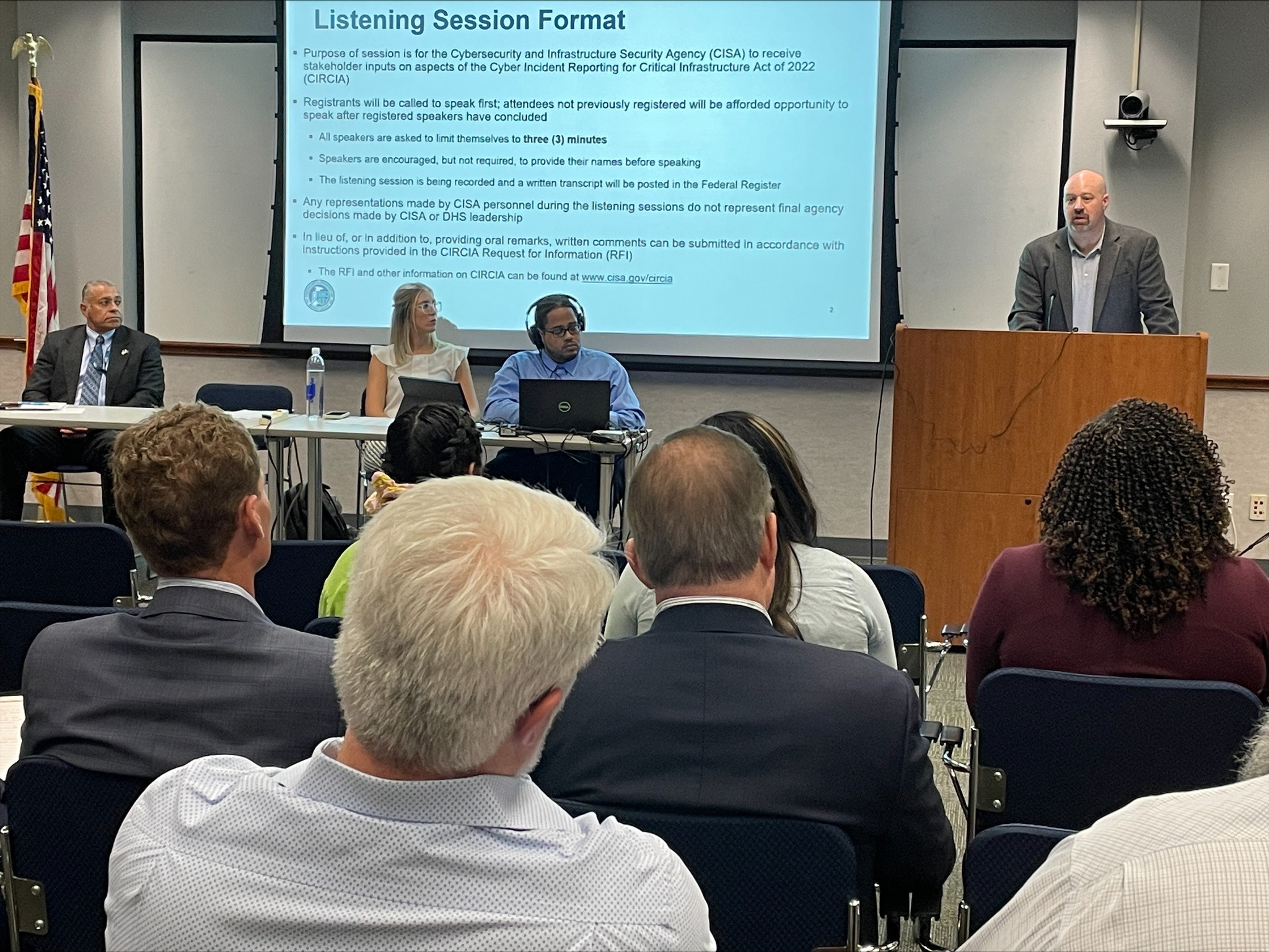
Second, CISA is also offering a series of public listening sessions – free events in which the public is invited to talk to CISA representatives about the new rules. These sessions have already begun and are coming to cities across the country, with the final session currently scheduled for November 16 in Kansas City.
Session attendees can maximize their impact by preparing their remarks in advance. The advice for written comments above applies to spoken comments as well.
Indeck said the public input period was a rare opportunity for the utilities industry to partner with CISA to establish clear and mutually beneficial guidelines for the sector.
“Whilst many states have mandatory reporting in place, as it currently stands, federal rules on reporting cyber incidents are voluntary… so of course, many utility companies aren't reporting.
“This is understandable, as reporting is not incentivized. Companies must consider the disincentive of added bureaucracy, and for those in the sector trying to do the right thing – well, it can be very frustrating.”
In the long-term, it’s important that rules are designed to not be overly burdensome, Indeck said, and that companies are confident they can report without fear of reprisal “for simply acknowledging that a breach happened”.
“It’s only with this kind of ‘no fault reporting’ that we can ever hope to encourage businesses that reporting is in everyone’s best interests.
“CISA is in an excellent position to foster this collaboration between public and private sector. However, it’s for this reason that it is important CISA be seen as an ally… and to ensure this, we
should leave the carrot in CISA’s hands and the stick in the hands of regulators – who already have the mandate to enforce as necessary.”
Timeliness will be critical to getting it right.
For reporting to be useful – in responding to malicious campaigns or ensuring that the 'blast radius' of incidents is quickly contained – Indeck said that information should flow as quickly as possible.
“However, this needs to be balanced with accuracy and completeness. If you report too early in an incident, the facts are likely speculative, at best… or entirely absent. And if you report too late, the reporting becomes much more detailed, but the window for action may be long past.
“Some recently proposed rulemakings by both regulators and lawmakers have suggested a model of an initial report as soon as it is practicably possible, followed up with a much more detailed report up to 30 days later, once the investigation has reached an adequate state of maturity. This indeed may be the best approach, but will require careful balancing between the needs of all stakeholders.”
And, he said – it was of critical importance to get this balance right.
“The key is to support critical infrastructure companies to report the most pertinent, actionable information that has value across critical infrastructure, rather than to just send tons of unfederated and un-useable data”
“Ultimately there is an opportunity here to shape the landscape in a way that can help prevent the increasing escalation in attacks against our critical infrastructure and better protect our nation and its economy. However, to get there we need ensure that all parties are at the table –and that can only be achieved through active collaboration.
Indeck encouraged all critical infrastructure companies with the ability to contribute to the conversation to do so.
“This is a chance for both regulators and the regulated to come together to impact our national security – and for utilities to have a voice in defining cyber incident reporting procedures,” he said.
Build tougher defenses
To reduce the likelihood of writing more reports, operators should also aim to deflect cyberattacks before they become a reportable incident. Indeck said that the most secure cyber defense systems available today for critical infrastructure facilities is not traditional software security – such as firewalls - but a new breed of cybersecurity known as ‘hardware-based security’.
“Of course, operators should make their voice heard through the public consultation process. They should also look at building tougher defenses against breaches. Look into what updates you can make to protect your organization, such as hardware security protections like Q-Net Security.” he said.